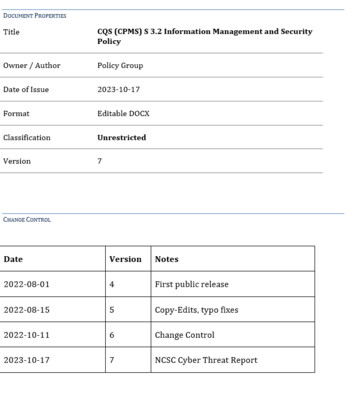
CQS (CPMS) Information Management and Security Policy
The recent update to the Core Practice Management Standards (CPMS) requires CQS firms to have a policy in place in relation to Information management and security (s3.2).
Policy documents can be time-consuming and difficult to prepare.
The Information Management and Security Policy includes reference to:
- General Data Protection Regulation (GDPR)
- Information Risk Management
- Information Asset Register
- Collection and distribution of data
...as well as other formalities and general obligations as required under 3.2 of the CPMS.
CONTENTS Document Properties Change Control Associated Policies Contents 1. Introduction 2. Responsibilities 3. General Data Protection Regulation (GDPR) 3.1 Overview 3.2 Data Protection Principles 3.3 Grounds for Processing Personal Data 3.3.1 General 3.3.2 Client Personal Data 3.3.3 Employee Personal Data 3.3.4 Provision of Information to Data Subjects 3.4 Sensitive Personal Data 3.5 Purposes of Processing Personal Data 3.6 Categories of Individuals Whose Personal Data is Processed 3.7 Recipients of Personal Data 3.8 Categories of Personal Data Processed 4. Information Risk Management 5. Information Asset Register 6. Information management principles 7. Collection and distribution of data 7.1 Collection and use of data 7.2 Distribution of data 8. Storage retention and disposal of information assets 9. Intellectual property of others (copyright) 10. Confidentiality and the authorisation for disclosures 11. Information security threats 11.1. Scope 11.2. Types of threats 12. Information security measures 12.1 Backup of Data 12.2 Physical security of paper-based records 12.3 Use of USB drives 12.3.1 Physical security of IT equipment 12.4 Procedures for detecting and removing malicious software 12.5 Preventing the misdirection of emails 12.6 Preventing the misdirection of paper records 12.7 Dealing with enquiries 12.8 Use of firewalls 12.9 Management of user accounts 12.10 Information security and data protection training 12.11 Bank account security 12.11.1 Receipt and transmission of bank details Transmission of bank details Checking bank details of other Conveyancers and third parties 12.11.2 Spoof transfer requests 13. Register of software 14. Data Subject Access Requests 14.1 General 14.2 Fees 14.3 Procedure 14.4 Unfounded and excessive requests 15. Cybercrime prevention procedures 15.1 User Level Prevention 15.2 ‘Senior Personnel/Business’ Prevention 15.3 Cyber Threat Report Guidance
Exclusions to note
Sample template bundles do not include a template to show the structure of the residential conveyancing department at a firm. The data protection policy template covers the requirements of CQS, however it is the responsibility of the firm to ensure it is compliant with the requirements of the General Data Protection Regulation.
All prices are plus VAT.